What is Email Threats??
The rapid development of human reason influencing and influenced by information technology can no longer be dammed, especially in the age of progress as it is today when humans create computer technology at the same time. The Internet is a commercial community activity to be the largest, and fastest growth that has transcended the boundaries of a country. With the internet through the network then we can know what is happening today in other parts of the world.
With the internet world or also called cyberspace, almost everything can be done. The positive aspect of the virtual world is of course shaping the world's technological development trend with all forms of human creativity. But the negative effects can not be avoided, for example in the form of pornography rampant in the Internet media.
The development of Internet technology led to a crime called cyber crime or crime through the Internet network. The emergence of several cases of cyber crime in Indonesia, is a phenomenon, such as credit card theft, hacking against various sites, tapping the transmission of data of others, (eg email), and data manipulation by preparing unwanted commands into computer programmers. Various actions above can be subject to criminal acts, both formal and material offense. Formal delik because related to the actions of someone accessing other people's computer data without permission, while the material offense is the act that has caused harm to others.
Based on the motive of his activities, cybercrime can be classified into two types as follows
- Cyber crime as a purely criminal act
Pure crime is a crime is a crime committed because of the motive of criminality. This crime usually uses the internet only as a means of crime. An example of this kind of crime is carding, which is the theft of credit card numbers belonging to someone else for use in trade transactions on the internet. Also the use of internet media (webserver, mailing list) to spread pirated material. Anonymous e-mail senders containing promotions (spamming) may also be included in examples of crimes that use the internet as a means. In some developed countries, the perpetrators of spamming can be sued for alleged privacy violations. - Cyber crime as a "gray" crime
It is quite difficult to determine whether it is a crime or not considering the motive of his activities sometimes not for crime. Probing or portscanning, for example, for surveillance of other people's systems by gathering as much information as possible from the surveillance system, including the operating system used, the ports, either open or closed, and so on.
Based on the crime target cyber crime can be grouped into several categories as follows:
- Cybercrime that attacks the individual (against person), this type of crime, the target of the attack is addressed to individuals or individuals who have certain characteristics or criteria according to the purpose of the attack, for example: (a) pornography, by making, installing, distributing and distributing materials that smell pornography, obscene, and expose inappropriate things; (b) cyberstalking, to harass or harass a person by using a computer, for example by using repeated e-mails as well as terror in the cyber world. The disorder may be sexual, religious, and so forth; [c] cyber-tresspass, with which it violates the privacy of others such as web hacking. breaking to PC, probing, port scanning and so forth.
- Cybercrime attacks property rights (againts property), ie cybercrime done to disrupt or attack the property of others. Some examples of such crimes include unauthorized access to computers via the cyber world, the possession of unauthorized electronic information / information theft, carding, cybersquating, hijacking, data forgery and all activities that are detrimental to the property of others.
- Cybercrime attacks the government (againts government); this is done with the specific purpose of attack against the government. Such activities such as cyber terrorism as an act that threatens the government, including cracking to the official government website or military site.
The things mentioned above require legal arrangements. Many countries do not yet have specific legislation in the field of information technology. Then how to solve a variety of computer crimes associated with the applicable criminal provisions because the criminal provisions that regulate the crime of computers that are currently in effect is still not complete. The legal tools in IT are still weak. Similarly, the crime of pornography on the internet, for example the Criminal Code Article 282 requires that the element of pornography is considered a crime if done in a public place. In Indonesia there is no article that can be used to trap cybercrime criminals. For the case of carding for example, the new Police can trap the perpetrators of computer crime with Article 363 theft because the suspects do steal credit card data of others.
But in this article I will discuss about crime in email or email threats
Kontributor:
Putri Sema Perdana
The threat of Email Crime
The use of corporate email generally aims to: separate personal affairs and job matters, to look professional and reliable in the presence of business partners, to improve the productivity of the company as well as formal business communications.
Spamming
In general, spam contains content content about the promotion of various products and services. Usually a lot of us know as spam is inbound spam, or spam that goes into our mailbox. If we look at the flow, spam is divided into inbound spam and outbound spam.
Inbound Spam - Inbound spam or spam we used to know. This is a junk email that needs to be filtered so that our email storage is not full fast and important information is not missed. Prevention is by implementing Enterprise Anti Spam & Virus on your Mail Server and doing Bayesian learning against new spam-spam.
Outbound Spam - Outbound spam is a spamming activity done by your Mail Server. Spam submission is done by email accounts that have experienced a breach security so that it can be accessed by hackers to send spam using the email account. Outbound spam events do not recognize the time, can occur during the day or night. We can imagine in the middle of the night, our email account suddenly sends thousands of emails even hundreds of thousands of emails per hour. What will happen?
The email server will be busy sending multiple emails, even under certain conditions email server will die suddenly. If the email server is dead, business communication is interrupted. IP Server Reputation is bad
When the IP server's reputation becomes bad, the mail server will be listed in the blacklist sender. Where many email servers will check the database blacklist this sender. If the server's reputation is bad, then the email from the server will be rejected.
Outbound spam can be prevented in several ways as follows.
Personally, everyone needs to change the password periodically. Periodic malware scan needs to be done on the device used by every email user. In terms of email infrastructure need to implement mail security that can detect self-spam outbound activity. Configure the email server to restrict unnatural email delivery.
Here are some ways you can take steps to reduce spam
- Do not include your main email into a newsgroups, mailing list, newsletter or chat room. Spammers use a software that runs 24 hours (spots or bots) and logs into a mailing list, chat room, which searches for email addresses. If indeed you are forced to use email, write with words, for example email budi@anduk.com be mindful at anduk dot com
- Give your primary email address only to friends / colleagues you trust. If you are not familiar (either online or offline), just give your free email address for example: Yahoo Mail or Google Mail (including sales / SPG who handed the form to fill in your e-mail address). Given the number of internet users who are still beginners who try to sell your email address to companies that need a lot of email address list for the purposes of promotion
- Do not use common names or common words in email creation. Spammers use a program that creates random names based on common names and words, common names and words they can get from book lists and dictionaries, which are then included in their program database.
- Do not answer even emails of any offer. If you have already received an email from an obscure company or address like this, delete it without replying. If you continue to receive these emails periodically, check them under the email. If there is an unsubscribe word, immediately click the word, and send it via email you receive the spam email so your email can be deleted from their database.
- If forced to fill your email address on a form on the internet as in a survey. Read carefully the policy provisions (privacy policy) of the website. If there are conditions that require you to receive some of their products, if they can not be included (not checked) so you do not receive their product.
Scamming
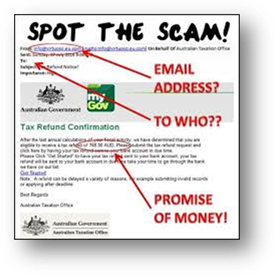
Email Scam usually contains a very convincing message. Scamming is similar to sms containing winning lottery information, "mama ask for credit", and the like. Such information is a form of scamming that is sent via SMS messages.
The form of scamming email is quite varied, generally it contains something interesting. Whether it attracts sympathy, attracts feelings of happiness. Where if you believe it, it will be stuck on a trap mechanism that will lead us to make "voluntary" payments, like hypnotized people.
Scamming email is rather difficult to avoid, anyone can just accept it, especially if the perpetrators of scamming perform its actions targeted at certain individuals. For that, need vigilance in trusting information and of course to confirm several times to the parties concerned.
Phishing
Phishing if spoken is similar to the word fishing, or fishing activities. The decisive factor in fishing success is the right target feed. A really interesting feed, a feed that's really similar to a natural food target. In phishing email, the feed is fake information that seems to be similar to reality. It is usually delivered as if from an authority such as a System Administrator, a Bank Officer etc.
Such information may be an invitation to update the targeted account information. Usually the information content is very convincing and contains an information update form.
As an example. Here is a Phishing email that seems to be in the name of Zimbra Administrator, the feed provided is that your mailbox is full and needs to validate the account. This content contains the URL of the information update form.
What happens if it gets hooked?
If the account is targeted paypal account then it can experience financial losses. If the account is targeted to an email account then there will be an abuse of the account. Misuse of one's account is used for outbound spam delivery.
For that, it is necessary to carefully receive information and confirm several times to the parties concerned. If you receive a scamming email, immediately report to the system administrator for scamming email content is learned as spam. So in the future the email content does not go back into the inbox.
System administrator email also need to add SPF record and perform certain configuration on Anti spam and mail server, so that one can not on behalf of domain name of company
Malware Propagation
The world of email and internet communications sometimes feels full of the dangers of malware, viruses. The corporate email system may already have anti-spam and anti-virus software to protect email from viruses. But the software can not prevent all malicious emails and some malicious threats coming from the internet, among them:
- Trojan horses
- Virus
- Worms
- Spyware
- Ransomware
In addition to applying complicated passwords to every email account, here are the things that can be done to avoid malicious emails. Always update the Anti-virus used in the computer. An anti-virus update can avoid you from the latest viruses and malware. Never ever:
- Opening emails from unknown senders
- Click any link, except trusted links
- Opening attachments except from trusted sources. Perform an Anti virus scan before opening it.
Spoofing
Many have applied the basic of email security, so why keep watchful? Hacking an email account is so common that it can almost daily get emails from a known person whose account has been hacked. So, even if you recognize the email address, do not immediately believe in the contents of the email. Do check and re-engage with the person concerned.
Spoofing Email uses a fake "From" address. If you receive an email from the CEO of the Company, or from the Clinic of a doctor requesting some of your personal data. Any emails requesting personal data should be wary of malicious emails.
Contact the sender through other media to confirm the request before submitting sensitive information. Do not confuse sensitive data such as passwords, account numbers, credit card information and so forth before getting a convincing confirmation.
These email-based crime threats can be prevented by performing certain configurations so that the email system becomes secure and reliable. In addition, email users should also awareness to always be alert to every email and do re-confirmation to some related parties and end device security is used by doing regular anti-virus updates.
How to overcome spoofing in emails are:
SPF is an email validation system designed to detect and block spoofed emails. SPF performs detection and email encryption by verifying the sender's mail server before forwarding mail to the recipient.
SPF allows users to specify which servers are allowed to send mail on their domain, and can provide information to be checked by the recipient. Domain owners can avoid using their domain for spoofing by creating an SPF record, which contains a list of domains or a valid IP address that has the authority to send mail for their domain.
From the recipient's email, the receiving server that has SPF checking facility can validate the sender's validity by checking the SPF record that has been created by the sending email domain.
Similar SPF procedures are also used by Microsoft Exchange email servers under the name "Sender ID".



![clip_image002[4] clip_image002[4]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEiDpaqaEtEqS6nnWzmY5bU2I62hmcxVlGKoiVdiB0DSqHiAK2ONWKY3K1o4rS71ipFKSGEg0uCOCC7igaebT3bSKjWWM8ymf2Td-qHC1VjrgbyvTe2mECeQQxToWAt_Kssv6sd-kXGmBvGX/?imgmax=800)
![clip_image003[4] clip_image003[4]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjCE1QZn4Ob2-AXxu_K8dJA5ymxtzBuTMGmO-KqvdkG9hsWFxu6ppUZTR41mvBKC40NEXxmCdJFnG7HX5o7J5nq-435ZIjH_5YZ7nWR4iijhv1mVtg7mWOcxgodFCpAQhkMR04Wa2Ru32c-/?imgmax=800)
![clip_image002[6] clip_image002[6]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEg2XojTX69ShaJdg9hEdsEtUIF39IeM6TyAJxQ1w2sWc46AewMtOriYWXcLJW7Kof8n-LJFVJ4k8uYsiUGkvFcTM_k0Ch0oY7W64Mp6Yysb0EKMR1HzxwYUUVQGbj69f8mu4Y2NXvnRoRUJ/?imgmax=800)